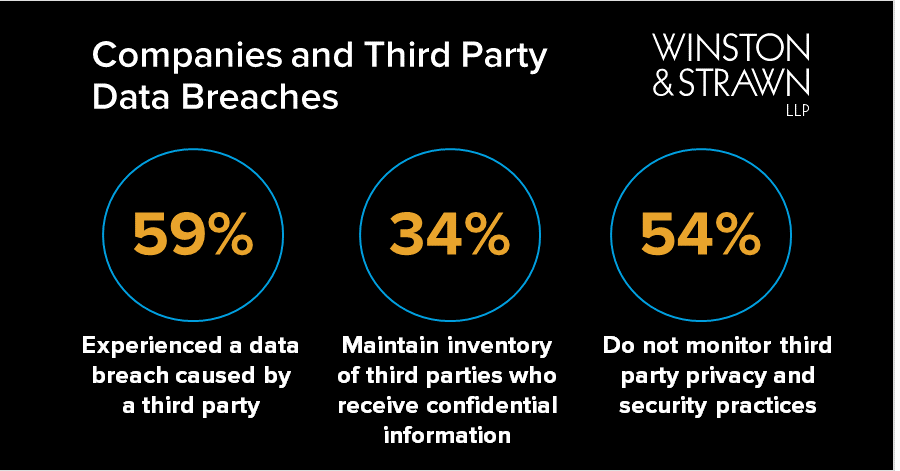
In the wake of a data breach, what are three important steps to avoid a repeat and establish long-term data security? - Wavestone

Only two percent of IT experts consider third-party secure access a top priority - Help Net Security

Gartner Says 52% of Legal & Compliance Leaders Are Concerned About Third- Party Cybersecurity Risk Since COVID-19